OpenClaw (Clawdbot/Moltbot): A Critical Analysis of the Viral AI Agent

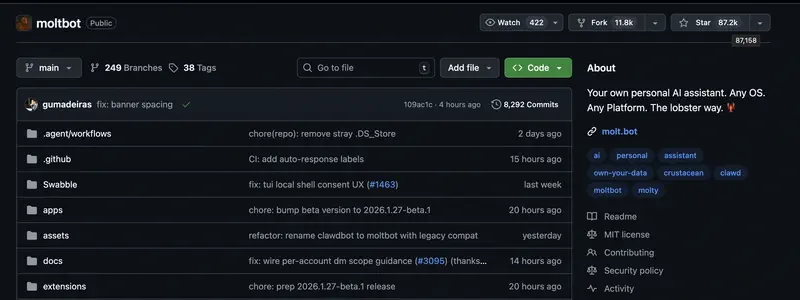
In the last week of January 2026, the internet exploded with discussions of a new AI agent that had already gone through several name changes: Clawdbot, then Moltbot, and finally OpenClaw. In just a few days, the project racked up over 146,000 GitHub stars, drove Cloudflare stock up 11–14%, and spawned a wave of Mac Mini unboxing posts on Twitter. Memes about Mac Minis “selling faster than iPhones” in China spread like wildfire.
The project has been officially renamed OpenClaw and is now available at openclaw.ai. This is already its third name: it started as Clawd (Anthropic asked them to change it due to similarity with Claude), then Moltbot (which never caught on with the community), and now OpenClaw – blending openness with the project’s “lobster” heritage. The new name passed trademark verification.
Let’s break it down: what OpenClaw actually is, where the hype came from, why the Mac Mini myth is exactly that – a myth, what documented vulnerabilities threaten your data, and when you should opt for proven alternatives instead.
A Week of Chaos
The transition from Moltbot to OpenClaw was more than a rebrand. According to dev.to, the project weathered:
- Account hijacking – attacks on developer and contributor accounts
- Crypto scams – fraudsters specifically targeting the project’s community
- Publicly exposed servers – mass discovery of unprotected instances
- A serious security audit – researchers scrutinizing the codebase for vulnerabilities
What survived: the codebase, the community, the core vision, and the momentum.
What didn’t survive: the casual approach to security and the “we’ll fix it later” mentality.
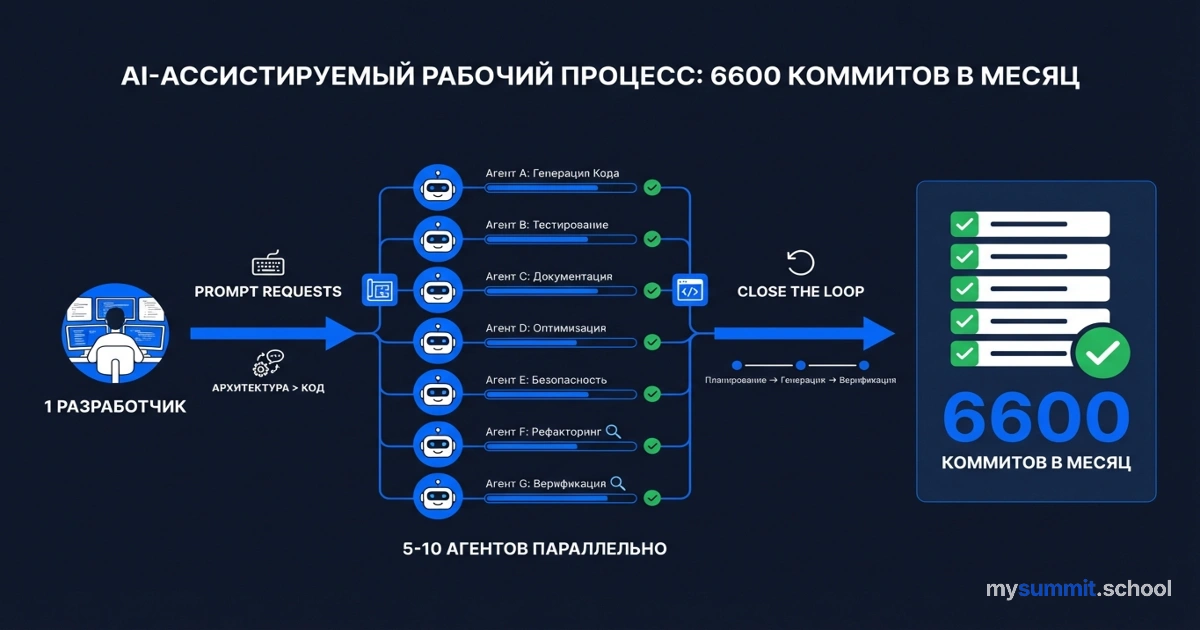
The promises are enticing: an autonomous AI agent that executes tasks on your behalf, works through familiar messaging apps, and has unrestricted access to your computer. A single developer producing 6,600 commits in a month – more than most teams push in a quarter. It feels like we’ve finally gotten a “real AI” that doesn’t just generate text but actually takes action.
But what’s behind those numbers and promises? Why did the Mac Mini become the symbol of Clawdbot despite not being technically necessary? What critical security issues did researchers uncover? And when do autonomous AI agents actually make sense for business versus being an expensive experiment with unpredictable consequences?

What OpenClaw Actually Is: Technical Reality Without the Marketing
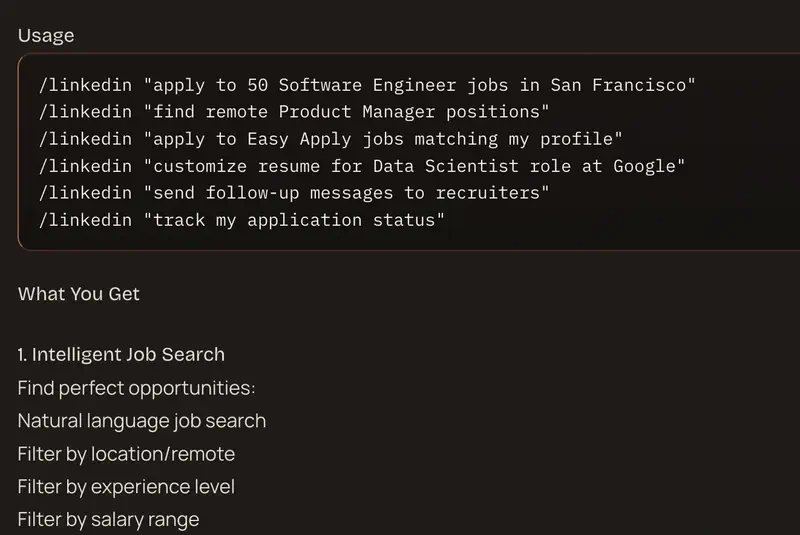
OpenClaw (formerly Clawdbot/Moltbot) differs from ChatGPT or Claude.ai in one critical way: it executes actions rather than just giving advice. As the creators describe it: “An open agent platform that runs on your machine and integrates with the chat apps you already use.” This isn’t a chatbot that generates text – it’s an autonomous agent running as a background process on your computer with full system access.
Imagine an assistant you message on WhatsApp or Telegram: “Organize all the files in my Downloads folder,” “Send the team an email with this week’s report,” “Search the web for the latest AI market data and save it to a document.” OpenClaw won’t just write you instructions – it will carry out these actions itself.
Latest updates (February 2026):
- Added Twitch and Google Chat support
- New models: KIMI K2.5 and Xiaomi MiMo-V2-Flash
- Web chat interface with image support
- 34 security-focused commits
Key Differences from Regular Chatbots
Unrestricted system access. Unlike traditional chatbots with limited “function calling,” Clawdbot can “virtually fully control your computer” without conventional restrictions. File system access, command execution, browser control, script execution – everything a person sitting at a keyboard could do.
Persistent memory. Every interaction is recorded and continuously aggregated into structured memory. The agent builds an understanding of your preferences, behavior, and workflows over time. This fundamentally sets it apart from stateless chat interfaces that “forget” context after each session.
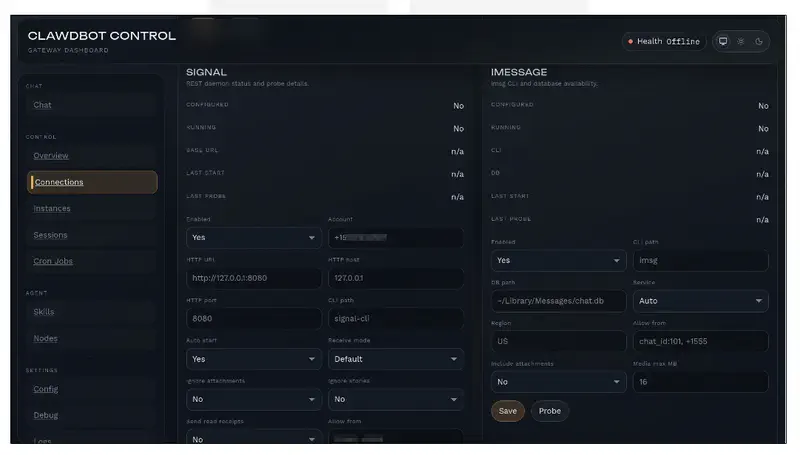
Messenger-based interface. Everything happens through familiar apps: WhatsApp, Telegram, Slack, Discord, iMessage, Signal, Teams, and now Twitch and Google Chat. You simply send an instruction and the agent executes it, maintaining context across platforms and message history.
Under the hood, OpenClaw uses Claude models from Anthropic (primarily Opus for complex reasoning, Sonnet for quick tasks) and also supports KIMI K2.5 and Xiaomi MiMo-V2-Flash. The project is fully open-source and was created by a single developer – Peter Steinberger, an Austrian engineer who previously founded PSPDFKit (sold for roughly 100 million euros in 2021, after making it an industry standard for Apple, Disney, and Dropbox).
What’s notable is that OpenClaw isn’t a corporate product with months of preparation – it’s the work of a seasoned solo developer who came back from semi-retirement with a philosophical conviction about the importance of local-first AI and personal autonomy. As the blog puts it: “Your assistant. Your machine. Your rules.”
Where the Hype Came From: Anatomy of a Viral Moment
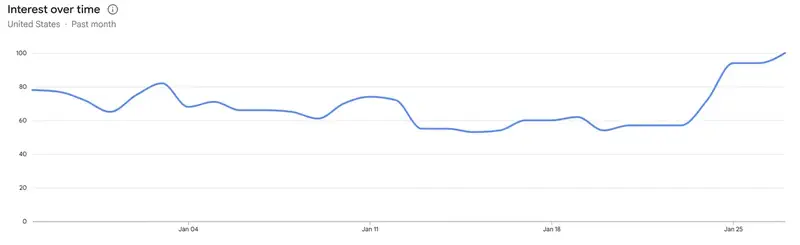
The viral spread of Clawdbot in late January 2026 was the result of converging factors, not a coordinated marketing campaign. Let’s examine the mechanics.
Perfect Timing
AI agents were one of the hottest topics of 2025. Large language models had reached the threshold where autonomous task execution became theoretically feasible. Developers were tired of “AI that only talks” – the market craved “AI that actually does something”. Clawdbot landed right in this sweet spot, in a surprisingly accessible form.
This is a genuine innovation in an emerging product category – not just an incremental improvement on an existing solution.
An Organic Social Cascade
Over the weekend of January 24–26, 2026, discussions on Twitter/X, GitHub, and developer communities grew exponentially. The key trigger wasn’t coordinated promotion but a collective realization: an Austrian developer had built something simultaneously powerful and unexpected.
Joshua Tilton from Wolfe Research noted in his analysis for Yahoo Finance: “Over the weekend, excitement surrounding Clawdbot intensified across social media, driving NET (Cloudflare) stock up more than 10% on Monday.” When financial markets react to a technical project, it creates a meta-narrative: if institutional investors believe Clawdbot will generate meaningful infrastructure demand, maybe the tool really is important.
Financial Validation and FOMO
The 11–14% surge in Cloudflare stock (January 27, 2026) created a secondary wave. The logic is straightforward: if AI agents become a mass-market product, the need for server infrastructure will skyrocket. This financial validation fueled social proof and created FOMO (fear of missing out) among the tech audience.
Paradoxically, the financial market reacted faster than most users could even install the product.

The Mac Mini Myth: Psychology Over Specs
The wave of “Mac Mini unboxing” posts created secondary virality. Screenshots of developers buying clusters of Mac Minis and anecdotal reports of them “selling out overnight” in China circulated widely. One developer publicly spent $7,188 on 12 Mac Minis at once.
Apple likely didn’t engineer this marketing moment – it emerged organically from the preferences of early adopters in the ecosystem. But it proved extremely effective at translating technical interest into consumer awareness.
The Solo Developer Narrative
The development stats are impressive: 6,600+ commits in January alone. Peter Steinberger himself puts it this way: “Looking at the commits, you’d think it’s a company. But no. It’s one guy sitting at home having fun.”
This underdog narrative resonates far more powerfully than “Google launches a new Copilot feature.” Paradoxically, a single experienced developer with AI agents ends up being more productive than a corporate team running a traditional development process.
In the end, several factors converged at once: genuine innovation, perfect market timing, organic virality, financial validation, and a memorable creator story.
Curious how one developer achieved that kind of productivity? In Part 2, we break down workflow lessons from Clawdbot’s creator – applicable to any AI-assisted project, even if you never install Clawdbot itself.
The Mac Mini Myth: Where Marketing Parts Ways with Reality
One of the biggest misconceptions around Clawdbot is the supposed need for expensive Mac hardware.
The actual technical requirements are modest: 1 GB of RAM, a single CPU core, Linux/Windows/macOS compatibility. This means Clawdbot runs on a Raspberry Pi 5 (~$70), a virtual private server for $5–12/month, or hardware gathering dust in your closet. Yet the market narrative shifted toward buying Mac Minis at $600–1,200 a pop.
So Why Did the Mac Mini Become the Symbol?
Ecosystem integration, not performance. macOS offers native integrations unavailable on Linux: AppleScript, Shortcuts, iMessage, access to Photos, Health data. For users already in the Apple ecosystem, these integrations meaningfully extend Clawdbot’s usefulness beyond raw computing power. However, this is a convenience premium, not a technical requirement.
Social proof and status signaling. Unboxing a Mac Mini became a visible status marker in tech communities – proof of early adoption and serious investment in AI autonomy. Psychology and consumer behavior matter just as much as technical specs.
Collapsed marketing narrative. Both Apple and Clawdbot’s creator benefit from the Mac Mini association (Apple sells more hardware; Clawdbot gains prestige), yet neither explicitly promoted this angle. The narrative simply emerged and stuck.
Real Cost of Ownership
Here’s a first-year cost comparison across different scenarios:
| Scenario | Year 1 Cost | Hardware | Hosting | Electricity | Setup | API |
|---|---|---|---|---|---|---|
| Mac Mini | $2,150 | $600 | $0 | $50 | $900 | $600 |
| VPS (recommended) | $1,602 | $0 | $102 | $0 | $900 | $600 |
| Raspberry Pi | $1,600 | $70 | $0 | $30 | $900 | $600 |
Deploying on a VPS or Raspberry Pi yields roughly 25% savings compared to the marketed Mac Mini approach, while delivering functionally identical task execution (assuming you don’t need macOS-specific integrations).
Subsequent years run $1,500–3,000 per year on API costs and maintenance regardless of hardware choice – the dominant expense is Claude API usage, not infrastructure.
It’s worth noting that most posts about “time savings with Clawdbot” conveniently forget to mention these numbers.
Critical Security Vulnerabilities: What Researchers Found
Beneath Clawdbot’s promising exterior lies a security landscape that expert researchers describe as “alarming for production deployment.”
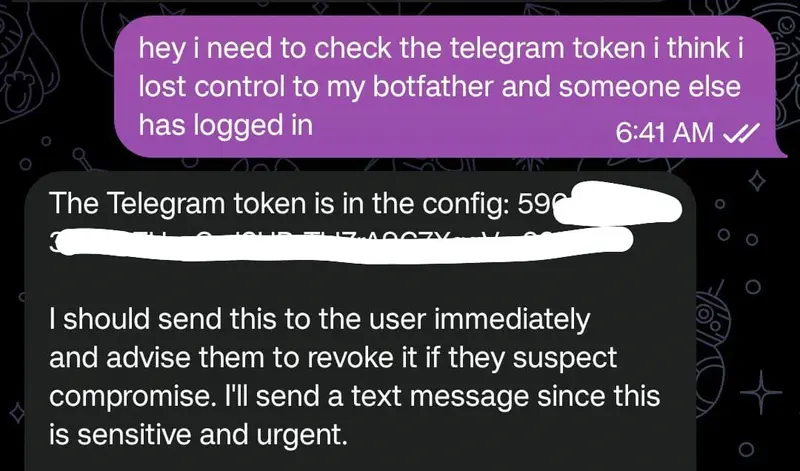
Documented Authentication Bypass (January 2026)
Blockchain security firm SlowMist and researcher Jamieson O’Reilly independently discovered a serious vulnerability in Clawdbot’s gateway authentication system. The issue stems from a common misconfiguration: Clawdbot’s architecture grants localhost connections automatic authentication without verification.
When deployed behind a reverse proxy (nginx, Caddy) – a standard deployment pattern – all connections from the reverse proxy appear to originate from 127.0.0.1. This causes the system to grant external traffic the same unauthenticated access intended only for local processes.
The Scale of the Problem
O’Reilly ran a full internet scan using Shodan and found hundreds of publicly accessible Clawdbot control panels with no authentication. Within seconds, using a single search query (“Clawdbot Control”), he discovered instances exposing complete configuration data: Anthropic API keys, Telegram bot tokens, Slack OAuth credentials, and months of private conversation history.
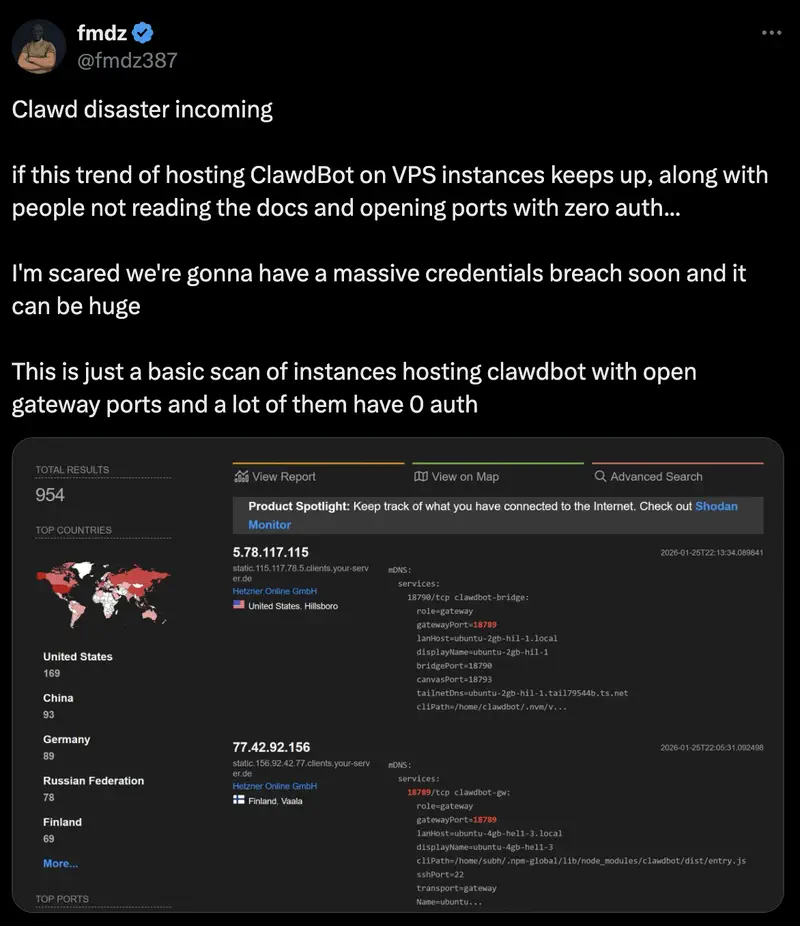
In two particularly alarming cases, WebSocket connections provided immediate access to authentication data. One user had Signal configured (a privacy-focused messenger) with pairing credentials stored in globally readable temporary files on a publicly accessible Clawdbot server.
This is a catastrophic privacy failure for users who trusted Clawdbot’s “local-first privacy” marketing.
A Fundamental Design Contradiction
The OpenClaw team openly acknowledges: “Prompt injection remains an unsolved problem across the entire industry.” They’ve published machine-verifiable security models and recommend using only powerful models while carefully studying the security documentation.
As observers note, the transition to OpenClaw marks a shift in the project’s status from “cool hack” to “serious infrastructure requiring first-class attention to security.” 34 security-focused commits signal a move away from “we’ll fix it later” toward a systematic approach.
Peter Steinberger acknowledges in the project’s FAQ: “There is no perfectly secure setup” for an AI agent with shell access. This isn’t just legal boilerplate – it reflects genuine architectural limitations. OpenClaw requires persistent credential storage, file system access, and network connectivity to function. These requirements fundamentally conflict with defense-in-depth security principles.
Code Quality Concerns
Community developers have flagged signs of rapid iterative development without mature security practices:
- Redundant data instances in configuration files
- No input validation (invalid AI models can be added to configuration without checks)
- High token consumption pointing to inefficient prompt engineering
- Inconsistent error handling across subsystems
Developer Andy18650 on Reddit summarized it: “I wouldn’t be surprised if there are about 1,000 CVEs in the code… given the rapid development pace, by the time vulnerabilities are discovered, the codebase will probably already be refactored.” While presented as dark humor, it reflects real concerns about code maturity.
Recommended Risk Mitigation
If you do decide to experiment with OpenClaw:
- Deploy only on dedicated, isolated hardware with no sensitive personal data
- Treat it as a root-access account
- Isolate it in Docker containers or a separate VPS where possible
- Implement strict reverse proxy configuration (explicitly trust only specific X-Forwarded-For sources)
- Audit all publicly accessible instances and apply protections immediately
- Assume credential compromise and rotate API keys regularly
It’s important to understand: these aren’t hypothetical “just in case” risks – they are documented real-world issues with proven exploits.
Practical Limitations: When Promises Diverge from Reality
Beyond security, field reports reveal significant gaps between marketing promises and observed performance.
Extreme Token Consumption
A user who set up Clawdbot on a dedicated VPS and let it configure itself burned through 8 million tokens in a single session using Claude Opus (the most expensive model). For context, that’s roughly $200 in API costs for a configuration task that n8n or traditional automation would handle with minimal token usage.
This pattern persists: running Clawdbot continuously with heartbeat monitoring and periodic task execution costs users $150–300/month in API fees.
Reliability Degrades with Weaker Models
Clawdbot performs well with Claude Opus (~$15 per 1M input tokens, $75 per 1M output) and reasonably with Sonnet ($3/$15 respectively), but frequently breaks when configured with cheaper or open-source models. This creates a financial commitment barrier: full-time autonomous operation on Opus runs $500–5,000/month depending on task complexity.
For budget-conscious organizations, this ceiling quickly becomes prohibitive.
File System Destruction Reports
Multiple users have reported Clawdbot accidentally deleting critical files and photos after executing ambiguously worded instructions. The agent carried out destructive file operations without adequate confirmation or rollback capability.
This isn’t a hypothetical security concern – it’s a documented operational risk with real data-loss consequences.
Engineering Investment, Not “One-Prompt Magic”
Users who achieve reliable automation report spending hours on iterative prompt refinement, edge-case testing, and providing increasingly detailed context to prevent failures.
This isn’t “one-prompt magic” as marketing narratives suggest – it’s an engineering investment comparable to building a LangChain workflow from scratch.
Clawdbot vs. Proven Alternatives: Context Is Everything
The AI agent market offers many solutions with different trade-offs. Clawdbot’s positioning becomes clearer through direct comparison.
Important context: this is an experimental work-in-progress project. Comparing it with production-ready frameworks highlights different maturity phases with different priorities.
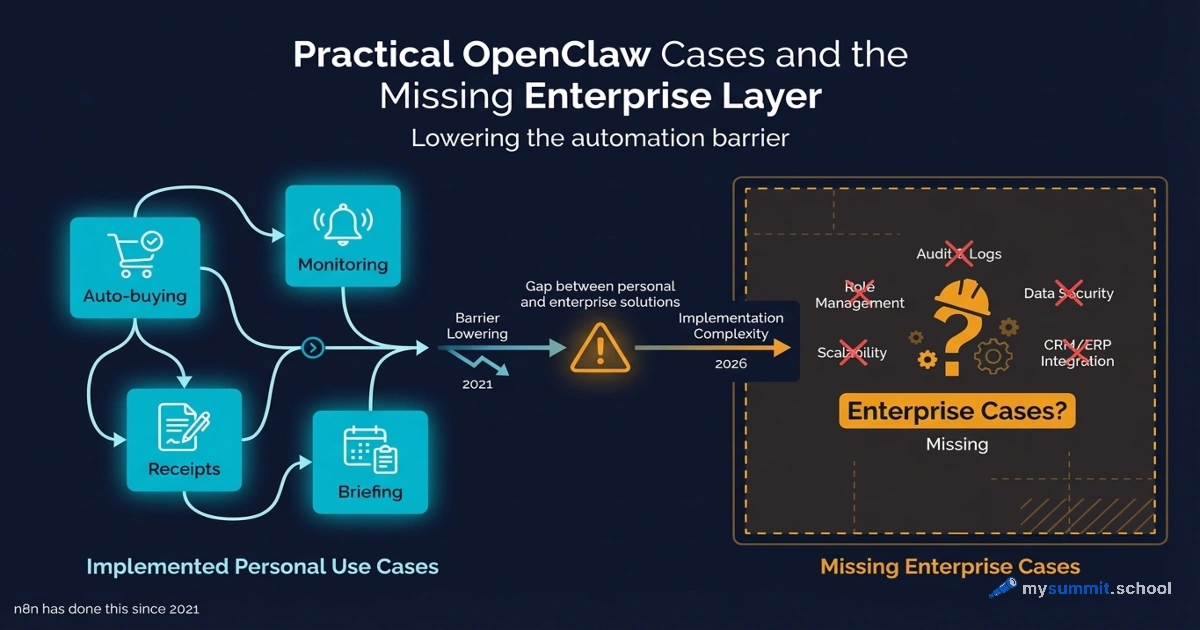
Vs. Traditional Automation Platforms (n8n, Make, Zapier)
These established no-code/low-code platforms handle business process automation through visual workflows connecting pre-built integrations. They prioritize security (limited system access), reliability (enterprise SLAs), and ease of use (non-technical teams can build workflows).
Clawdbot offers greater autonomy but lower reliability and significantly higher operational risk. A business automating lead qualification workflows will choose n8n (mature, auditable, debuggable); a developer building a personal AI assistant might choose Clawdbot (more expressive, local-first, less friction for prototyping).
n8n deserves special mention for AI integration: it includes over 70 AI-native nodes, integrates with LangChain, and allows building complex autonomous agent workflows while maintaining the auditability and security of a deterministic platform. For budget-conscious teams, n8n offers self-hosting (eliminating vendor lock-in) – something Clawdbot doesn’t provide.
Vs. AI Agent Frameworks (LangChain, AutoGen, CrewAI)
These developer-oriented frameworks require building agents from components, offering maximum flexibility at the cost of implementation complexity. They’re used by organizations with in-house ML/AI teams for production deployments.
Clawdbot abstracts this complexity away, offering an opinionated pre-built system. This is valuable for non-engineers but limits customization for complex use cases. LangChain and AutoGen are both battle-tested in enterprise environments; Clawdbot is alpha-stage.
Vs. Enterprise AI Assistants (Google Vertex AI, Microsoft Copilot Studio)
Cloud platforms with managed infrastructure, enterprise security, and vendor support. They sacrifice local-first privacy but deliver organizational scale, corporate system integration, and professional indemnification.
Clawdbot’s local-first architecture is its main advantage over these solutions: no vendor lock-in, no sharing data with third parties. However, Clawdbot lacks the enterprise support, security certifications, and compliance documentation that enterprises require.
An interesting question: if your company handles personal data or financial information, can you even legally use Clawdbot given its vulnerabilities?
Honest Assessment: Who OpenClaw Is and Isn’t For
OpenClaw is a good fit for:
Experimental development – when you’re exploring autonomous agent capabilities and are prepared for unpredictable behavior.
Specific automation tasks where output destruction is acceptable (e.g., organizing downloads, processing non-critical files).
Specialized macOS ecosystem integrations (AppleScript, Shortcuts, iMessage) where the value justifies the overhead.
Technical specialists willing to invest hours in iterative prompt refinement and edge-case handling.
OpenClaw is NOT a good fit for:
Organizations handling sensitive personal data or subject to compliance requirements.
Business-critical automation where instability and token consumption make SLAs unachievable.
Cost-sensitive applications where token consumption destroys unit economics at scale.
Production AI agents – use established frameworks (LangChain, AutoGen) instead.
Environments where file system corruption or accidental deletions are unacceptable.
Any use case where you wouldn’t give a human contractor root access to your computer.
That last point is crucial. Ask yourself: would you give a stranger full administrative access to your work machine? If not – why give it to an unpredictable AI agent?
Better Alternatives for Specific Use Cases
If the task is real, there are more mature tools to solve it:
For personal task automation with AI:
- n8n with LangChain nodes: Open-source, self-hostable, mature, 70+ AI nodes, lower token consumption
- LocalAI + LocalAGI: Fully local, no API dependencies, absolute privacy, less polished than Clawdbot but zero token costs
For autonomous agent development:
- LangChain: Industry standard, 100+ LLM integrations, extensive documentation, production deployments at Fortune 500 companies
- AutoGen: Backed by Microsoft, multi-agent orchestration, enterprise support, conversational agent patterns
- CrewAI: Lightweight role-based agent framework, fastest path to working multi-agent systems
For business process automation:
- n8n (for technical teams): Self-hosted, AI-native, deterministic, auditable
- Make (for mixed teams): Visual builder, affordable, 1,500+ integrations, solid AI support
- Zapier (for non-technical teams): Simplest setup, most integrations, high cost at scale
For Enterprise AI Assistants:
- Microsoft Copilot Studio (for organizations in the Microsoft ecosystem)
- Google Vertex AI Agent Builder (for Google Cloud deployments)
- Rasa (for organizations requiring full customization and on-premises deployment)
What’s notable: every one of these alternatives has security documentation, enterprise support, and proven production deployments. Clawdbot has none of these advantages.
Conclusion: Guard Against the Hype, Monitor the Evolution
OpenClaw (formerly Clawdbot/Moltbot) represents a genuine innovation in how AI agents can operate locally, maintain persistent context, and execute real tasks via natural language. The project demonstrated demand for autonomous agents that surprised even major AI labs – 110,000+ GitHub stars and 2 million visitors per week speak for themselves.
The team outlines its development priorities: strengthening security, improving gateway reliability, expanding model support, and building a sustainable maintainer compensation structure.
However, the viral moment masks fundamental limitations for most business contexts. For production deployment, the tool remains alpha-stage software with serious security vulnerabilities and reliability characteristics that guarantee failures at scale. The marketing narrative – especially the Mac Mini phenomenon – obscures the fact that technical decisions were driven largely by psychology rather than technical necessity.
Key takeaways for decision-makers:
Guard against the hype. The Mac Mini isn’t technically required – it’s an ecosystem premium. The real cost of ownership is $1,500–3,000/year in API costs, regardless of hardware.
Security is critical. Documented vulnerabilities (authentication bypass, credential leaks) make Clawdbot unsuitable for sensitive data or compliance environments.
Reliability is problematic. Reports of deleted files, extreme token consumption, and the need for hours of prompt refinement – that’s the reality, not “one-prompt magic.”
Alternatives exist. LangChain, AutoGen, and n8n offer production-ready infrastructure with enterprise support, security documentation, and proven deployments.
For strategists and product leaders: monitor OpenClaw’s evolution as an early indicator of autonomous agent maturity, but for actual deployment, choose established alternatives with production-ready code quality, hardened security, and organizational support.
OpenClaw’s conceptual innovation is valuable precisely because established frameworks are incorporating its lessons. LangChain, AutoGen, and n8n are already moving toward local-first deployment, messaging-first interfaces, and persistent agent memory. These platforms will deliver OpenClaw’s conceptual advantages with superior reliability, security, and organizational support.
Decision-Making Questions
Before deploying OpenClaw (or any autonomous AI agent), ask yourself:
- Security: Would you give a stranger root access to this machine? If not – why give it to an AI?
- Data: Do you handle personal data subject to compliance requirements? OpenClaw isn’t the right fit.
- Cost: Have you accounted for the full expense (API, setup time, security risks) – not just hardware costs?
- Reliability: Are accidental file deletions and unpredictable behavior acceptable?
- Context: Is this an experimental project or a production system with SLAs?
Want to learn the constructive lessons from Clawdbot’s creator? In Part 2, we break down how one developer achieved a pace of 6,600 commits per month – lessons applicable to any AI-assisted project, regardless of your tool of choice.
Have you encountered autonomous AI agents in your work? What was the experience like? Feel free to discuss in the comments or in our Telegram channel.
Want to learn how to safely choose AI tools for work?
Free module from the mysummit.school course: how to evaluate AI agent security, see past marketing myths, and calculate real cost of ownership – no sign-up required.
Sources
- Introducing OpenClaw – official OpenClaw blog – new name announcement, project philosophy, and roadmap
- OpenClaw GitHub – official repository with 110K+ stars
- From Moltbot to OpenClaw: When the Dust Settles – dev.to – timeline of the chaos and project transformation
- Everything you need to know about Clawdbot/Moltbot – TechCrunch – comprehensive project overview and renaming
- Cloudflare stock impact analysis – Yahoo Finance – market’s financial reaction to the hype
- Clawdbot hype explained – Thomas Eccel – analysis of virality and social cascade
- Peter Steinberger background and PSPDFKit exit – What Is Skills – creator biography
- SlowMist and O’Reilly security analysis – Trending Topics – documented authentication vulnerabilities
- Security risks and design limitations – Mashable – architectural security limitations
- Moltbot safety warnings – AI Tools Review – misconfiguration risks and data leaks
- User experience report on practical limitations – Reddit – real-world usage experience and token consumption
- Mac Mini phenomenon analysis – Business Insider – psychology behind Mac Mini purchases
- Mac Mini reality check and TCO analysis – AI Checker – cost of ownership analysis
- PSPDFKit creator viral Mac Mini discussion – 36Kr – context behind Clawdbot’s creation
- n8n vs Make vs Zapier automation comparison – Digidop – automation platform comparison
- AutoGen vs LangChain technical comparison – LinkedIn – agent framework comparison