OpenClaw in 72 Hours: Vulnerabilities, Releases, and Architectural Limitations. February 2026
Remarkably, a project can go from “safe hobbyist tool” to a documented CVE scoring 2 out of 100 in just three days. That is exactly what happened to OpenClaw between January 30 and February 2, 2026 – security collapsed, the product accelerated, and architectural limitations became publicly acknowledged. The paradox: the more users you have, the faster fundamental problems surface.
In the first part of this series we dissected the project with a critical lens and debunked the Mac Mini myth. In the second part we covered workflow lessons from the creator. This article focuses on what changed in literally the last few days.
Vulnerabilities and Security Incidents
CVE-2026-22708: Indirect Prompt Injection
CVE-2026-22708 (indirect prompt injection) is the most serious technical vulnerability documented over the past three days. When OpenClaw’s browser skill scans compromised web content, malicious instructions with high attention weight can override the user’s original intent, potentially leading to arbitrary command execution. The vulnerability stems from the language model’s context integration mechanism and is amplified by the agent’s elevated privileges. Source: Penligent
ZeroLeaks Audit Results
A comprehensive security analysis using the ZeroLeaks tool revealed critical findings: OpenClaw scored just 2 out of 100 when tested with Gemini 3 Pro, with an 84% data extraction rate and a 91% injection success rate. The takeaway is sobering: system prompts, tool configurations, memory files (SOUL.md, AGENTS.md), and embedded information can be extracted with minimal effort. Source: The Decoder
Three Critical Infrastructure Incidents
Beyond individual vulnerabilities, three critical infrastructure-level incidents occurred:
The Shodan incident exposed hundreds of instances running with auth: "none" on public cloud providers (DigitalOcean, Hetzner, and others), revealing API keys, bot tokens, auth secrets, full conversation histories, and command execution access. This incident directly prompted the removal of the auth: none option in v2026.1.29. Source: NXCode
A malicious VS Code extension called “ClawdBot Agent” appeared on January 27 and delivered the ScreenConnect remote access trojan to developer machines, harvesting credentials and API keys. Source: NXCode
Malicious ClawdHub skills (14 downloads between January 27–29) masqueraded as cryptocurrency automation and wallet tools, delivering stealer malware via obfuscated terminal commands. One malicious skill appeared on the ClawdHub homepage before removal, dramatically increasing the likelihood of accidental installation. Source: Tom’s Hardware
The $16M Crypto Scam
A parallel $16 million crypto scam capitalized on the chaotic triple rebrand (Clawdbot -> Moltbot -> OpenClaw). Scammers seized the abandoned Twitter account @clawdbot within seconds, launched fake $CLAWD tokens on Solana, and briefly reached a $16 million market cap before crashing to zero. Source: NXCode
Product Releases and Changes
OpenClaw v2026.1.30 (January 31, 2026)
A developer-experience and model-diversity focused update:
- Shell auto-completion auto-setup for Zsh, Bash, PowerShell, and Fish significantly improves CLI usability
- Kimi K2.5 and Kimi Coding available for free out of the box – a strategic move that contrasts with how traditional platforms lock users into a single model
- MiniMax authorization support enables seamless model switching with a single login
- 6 targeted Telegram fixes: thread handling, HTML rendering, delivery context, reaction processing
OpenClaw v2026.1.29 (January 30, 2026)
A fundamental security reset with the permanent removal of the auth: "none" configuration option. The development team describes this change as “the most important security change in the project’s history,” forcing all deployments to implement either token-based, password-based, or Tailscale Serve authentication.
Additional breaking changes:
- npm package rebrand (moltbot@latest -> openclaw@latest)
- Extension scope migration (@moltbot/* -> @openclaw/*)
- Updated daemon installation process via
openclaw onboard --install-daemon
34 Security Commits
The releases included 34 security-related commits and machine-verifiable security models, signaling an acknowledgment of early criticism and a deliberate pivot toward enterprise-grade hardening. Source: Dev.to
Want to learn how to evaluate AI tool security?
No payment required • Get notified on launch
Critical Limitations and Architectural Findings
Beyond vulnerabilities, a number of structural limitations have been identified:
Prompt Injection – an Unsolved Industry Problem
Prompt injection remains an unsolved problem across the entire industry, not unique to OpenClaw. Developer Peter Steinberger explicitly noted that this attack vector is “well-documented and not yet solved,” recommending users employ more capable models and study security best practices. Security researchers (Wired, The Verge) emphasize that agents with administrative access are disproportionately vulnerable to these techniques compared to stateless chatbots. Source: Trending Topics
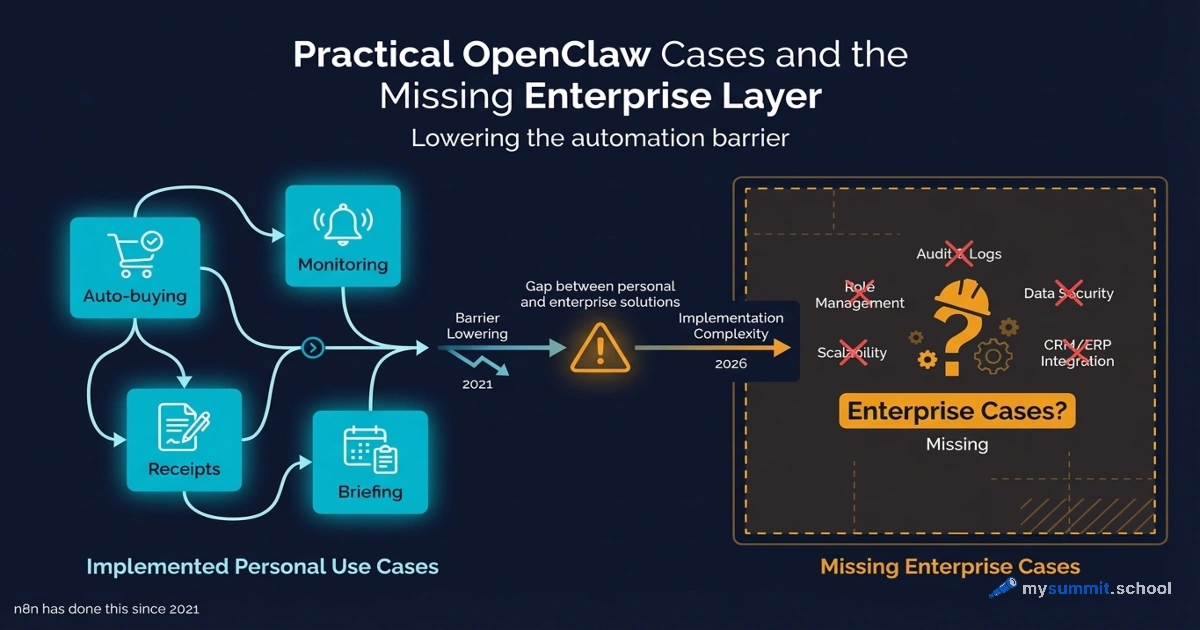
Cloud “Wrapper” vs. True Local Execution
OpenClaw’s claimed privacy advantage – running locally – is partly illusory. OpenClaw calls Anthropic Claude, OpenAI GPT, or other cloud APIs; it does not run frontier language models locally. True local execution (private models at Claude’s level on local hardware) remains technically infeasible in 2026 due to hardware constraints and compute requirements – that is a 2027+ reality. Source: NextWord Substack
Policy and Permission Gaps
Policy and permission gaps emerge as users demand more ambitious automation. OpenClaw lacks sophisticated guardrails for defining what agents are allowed to do, as opposed to what they choose to do within those permissions. This is uncharted territory requiring painful trial and error as the autonomous agent category matures. Source: NextWord Substack
Supply Chain Risks via ClawdHub
Supply chain risk through ClawdHub – OpenClaw’s community skill registry – exposes users who install third-party extensions to arbitrary code execution. Cisco’s demonstration of a malicious “What Would Elon Do?” skill showed active data exfiltration and direct prompt injection, although the root cause was user-installed malware rather than an internal OpenClaw vulnerability. Source: Serenities AI
Messaging Integration Attack Surface
The messaging integration attack surface spans WhatsApp, iMessage, Telegram, and Discord. Each messaging platform integration presents a potential entry vector for prompt injection attacks, expanding the agent’s external vulnerability.
72-Hour Summary
The last 72 hours have raised an uncomfortable question: can an autonomous agent with command-line access ever be hardened to enterprise-grade security? The project has moved from a weekend hobby (200K+ users in a week) to 34 security commits, yet researchers at Cisco, Penligent, and Vectra agree on one thing – the fundamental architectural tradeoffs (local autonomy + terminal access + credential integration) create inherent risks.
The security research consensus is clear: OpenClaw is not uniquely flawed; it is early, useful, and exposed. The next 90 days will determine whether the project can achieve the maturity in security policies, runtime guardrails, and monitoring tooling necessary for autonomous agents to become a sustainable infrastructure primitive rather than a security incident waiting to happen.
Strategic Pivot: From Hype to Hardening
The events of the last 72 hours mark a definitive shift in OpenClaw’s trajectory:
Forced security maturity. The permanent removal of auth: "none" in v2026.1.29 represents a pivot from “growth at all costs” to “mandatory security.” The project now sacrifices initial setup simplicity for baseline protection.
This raises a question: if basic authentication is a “sacrifice of simplicity,” how secure was the rapid growth phase with 200K+ users? Removing auth: "none" is less a strategic choice than a forced reaction to the Shodan incident that exposed hundreds of public instances with API keys.
Model democratization. Offering Kimi K2.5 for free out of the box directly addresses the “API cost” criticism. This steers the project away from dependency on expensive Western language models toward a more sustainable cost model for global users.
CLI utility as a competitive advantage. The focus on terminal auto-setup and developer convenience signals that OpenClaw is moving beyond the “Mac Mini” aesthetic toward becoming a genuine productivity tool for power users.
Expectation management. By publicly documenting systemic risks such as prompt injection and its “cloud wrapper” nature, the project transitions from an “AI miracle” narrative to a transparent identity as “user-controlled independent infrastructure.”
What This Means for Decision-Makers
If you are already using OpenClaw:
- Upgrade to v2026.1.30 immediately
- Verify that
auth: "none"is not in use - Review installed skills from ClawdHub
- Rotate API keys if your instance was publicly accessible
If you are considering OpenClaw:
- Recognize that this is real-time hardening
- Wait 2–3 weeks for security fixes to stabilize
- Alternatives (LangChain, n8n, AutoGen) remain more mature for production use
For strategic planning:
- OpenClaw demonstrates demand for local AI agents
- A “security-first” approach is now evident in the roadmap
- Conceptual innovations will be adapted by mature platforms
Series continuation: In the first part – a full critical analysis of the project, the Mac Mini myth, and an alternatives comparison. In the second part – workflow and productivity lessons from the creator.
Following OpenClaw updates? Join the discussion in the comments or on our Telegram channel.
Want to learn how to safely deploy AI agents?
Open module from the mysummit.school course: evaluating AI tool security, analyzing architectural risks, and choosing the right solutions for your business – no registration required.
Sources
- Penligent Security Post-Mortem – detailed CVE-2026-22708 audit and architectural recommendations
- The Decoder: ZeroLeaks Analysis – security testing results (2/100 score)
- NXCode: Complete Guide 2026 – Shodan exposure, VS Code malware, incident timeline
- Tom’s Hardware: Malicious Skills – ClawdHub malicious skill analysis
- Reddit: v2026.1.30 Release – official changelog, free models
- Dev.to: From Moltbot to OpenClaw – 34 security commits, transformation analysis
- Trending Topics: 2 Million Visitors – prompt injection as an industry-wide problem
- NextWord Substack: Ambient AI – local execution limitations, policy gaps
- Serenities AI: Cisco Research – supply chain risks via ClawdHub